The government is now looking closely at medical equipment cybersecurity. Will hospitals be even more regulated?”
By Heidi Horn
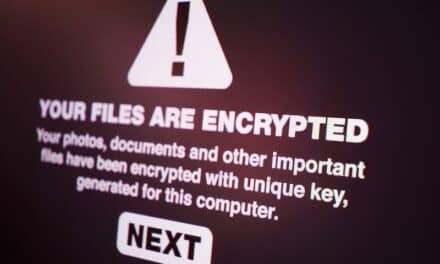
Driven by a dramatic spike in cyberattacks in recent years against hospitals, the government is now fully engaged in the discussion about how to best protect them.
The White House and Congress along with governmental agencies – including the U.S. FDA, the Department of Homeland Security, the U.S. Department of Health and Human Services (HHS), the Federal Trade Commission, and the FBI—are now all actively investigating the issue and making recommendations to mitigate the risks.
A ‘Critical’ Sector
In March 2023, the White House released its “National Cybersecurity Strategy” in which it references the protection of “critical infrastructures.” Healthcare is among the 16 critical infrastructure sectors identified by the government. The strategy document states, “While voluntary approaches to critical infrastructure cybersecurity have produced meaningful improvements, the lack of mandatory requirements has resulted in inadequate and inconsistent outcomes…Regulation can level the playing field, enabling healthy competition without sacrificing cybersecurity or operational resilience.”
This and other activities at the federal and state levels have left the healthcare technology management (HTM) community wondering if there may be more regulations headed our way surrounding medical equipment cybersecurity.
“It’s certainly a topic of conversation for many of us that lead HTM organizations,” says Barbara Maguire, vice president of quality and HTM at ISS Solutions Inc. “I think it’s not a matter if it will happen, but rather when it will happen.”
Carter Groome, MBA, CHISL, CFCHE, and CEO of First Health Advisory, agrees. He spends significant time in Washington, D.C., educating members of Congress and their staff about the state of healthcare cybersecurity and why it must be approached differently than other sectors.
“Overall, the White House can influence change, but passing a congressional bill is what will really move the needle,” Groome explains. “The guidance needs to become statute, and that’s where Congress will play their part. I think we could see some real movement in the coming months or the next Congress, with impactful, standard practices around cybersecurity that will directly impact HTM departments and patient safety.”
FDA Takes a Stance
Medical equipment manufacturers are already being held more accountable for protecting their products against cyberattacks. Spurred by a 2022 FBI report that found 53% of digital medical devices and other Internet of things devices in hospitals had known critical vulnerabilities, the FDA recently announced that it will require medical devices to meet specific cybersecurity guidelines.
Among the requirements, medical equipment manufacturers must submit a plan on how to “monitor, identify, and address” postmarket cybersecurity vulnerabilities and exploits, as well as create a process that provides “reasonable assurance” that the device and related systems are cybersecure, and make available postmarket updates and patches to the device and related systems.
In reference to the FDA’s announcement, Ty Greenhalgh, HCIPP, healthcare industry principal at Medigate by Claroty, calls it “an excellent step in reducing new risks to hospitals.” However, he concedes, challenges exist. “It doesn’t address the cybersecurity risk from millions of legacy medical technology devices, which will remain [in hospitals] for another decade.”
Both Groome and Greenhalgh have been members of HHS’ 405(d) Work Group and the Health Sector Coordinating Council’s Cybersecurity Working Group (HSCC CWG) since 2017. The Working Group produced “Cybersecurity Practices for Small, Medium, and Large Healthcare Organizations,” as well as the March 2023 release of its “Managing Legacy Technology Security” guide.
“The government and private sector are all working together in an unprecedented collaboration at never-before-seen speeds,” Greenhalgh says. “I would like to think this will be a collaboration of the best ideas involving the parties that are best suited to determine particular requirements.”
Groome concurs. “The policymakers in Washington do seem to be motivated in working across the aisle to benefit healthcare and the communities they serve,” Groome says. “There is clear common ground on providing support for improving patient safety, public safety, and ultimately national security.”
Those in the HTM industry are eager to find out what new laws and regulations may be headed their way. “There are so many vendors and guidelines these days that say they can solve all your medical equipment cybersecurity needs,” Barbara Maguire says. “The guidance documents from the HHS CWG provides a solid framework. However, [healthcare delivery organizations] shouldn’t wait for regulation. They should be asking their HTM providers what strategies they are employing today to ensure the security of medical devices they manage.”
Suffice it to say that Maguire practices what she preaches. “We’ve already incorporated training for all ISS Solutions technicians to ensure they understand their important role in medical device security,” she says.
Heidi Horn,MA, AAMIF, is president of Heidi Horn HTM Consulting. Horn has been an active member of the Association for the Advancement of Medical Instrumentation (AAMI) since 2005 and currently serves on the AAMI Board of Directors Executive Committee as treasurer.
References:
- https://www.whitehouse.gov/wp-content/uploads/2023/03/National-Cybersecurity-Strategy-2023.pdf
- https://www.cisa.gov/topics/critical-infrastructure-security-and-resilience/critical-infrastructure-sectors
- Source: Federal Bureau of Investigation Cyber Division September 12, 2022 report 220912.pdf (ic3.gov)
- Source: Cybersecurity in Medical Devices: Refuse to Accept Policy for Cyber Devices and Related Systems Under Section 524B of the FDC Act (fda.gov)
- https://405d.hhs.gov/
- https://healthsectorcouncil.org/
- https://405d.hhs.gov/Documents/tech-vol2-508.pdf
- https://healthsectorcouncil.org/wp-content/uploads/2023/03/Health-Industry-Cybersecurity-Managing-Legacy-Technology-Security-HIC-MaLTS.pdf