 |
One of the challenges of the increasing proliferation of IT-based medical equipment is that device repairs are much more challenging than in the past. Previously, a clinical engineer (CE) or biomedical equipment technician (BMET) could physically troubleshoot a device on-site and swap out failed components. This is still true, but often an issue may reside within software, device configuration files, etc, that CEs, BMETs, and even local vendor support may not be able to access. And even if they have access, they may not know how to modify the files to resolve the problem, or even be able to analyze the log files to determine the cause of the trouble. In addition, issues could be related to operating systems, third-party applications, or third-party hardware that vendors may utilize in their devices. Given the complexity of today’s computerized medical equipment and the security in place to protect those devices, relying on local vendor field engineers is no longer an easy or economical means to quickly resolve device problems in many cases.
Remote Access
Luckily, IT vendors have been providing remote support capabilities for years, and many medical device vendors have been able to leverage existing best practices for remote support. For a medical facility, remote support offers some very important advantages. First, it allows a facility to have access to a broader pool of experts. The vendor can pull in all these experts at any time without having to get them out to a specific site. This is particularly beneficial for remote sites that are not easily reached. Second, it allows the vendor to more proactively support its equipment. Vendors can often receive alerts of upcoming failures or can identify potential system issues before they become problems. The vendors can then resolve these issues remotely without any impact to the end users. Finally, remote support can offer significant cost savings for a facility, which no longer has to incur travel costs to have one or more vendor representatives travel to the site.
 |
| Remote support offers some very important advantages, such as access to a broader pool of experts. |
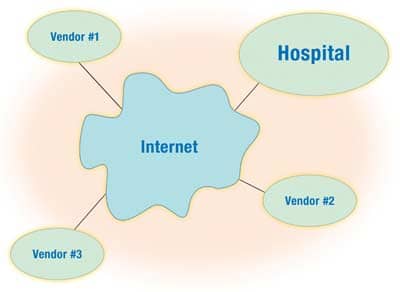
Now for the tricky part: Establishing remote connectivity is not an easy task. Historically, remote support was provided via direct modem connections to individual medical devices. However, many health care IT departments have outlawed the use of modems on their networks because they offer a significant security risk by allowing a potentially unsecured point of access to the hospital network. Some hospitals have established modem pools that vendors can dial into. These are generally controlled by the IT department so they can ensure that security restrictions are in place in terms of who can connect through those modems, and to what devices. Remote connectivity may be less of a security risk, but it poses a challenge for vendors in that they are typically connecting via a slow modem connection that does not provide the speed (or in some cases, availability) to make it convenient to provide remote support. As a result, many health care departments support remote access via some type of virtual private network (VPN) connectivity that essentially creates a secure pipe through the Internet between the vendor and the hospital. An IT department can then specify what individual devices can be accessed through that connection and/or what individual users have access to that connection.
To establish a secure VPN, each side would need to have a firewall in place to ensure that only desired access is provided through the VPN. Encryption would be needed to ensure that any data transmitted via the Internet would be unreadable if it were intercepted. A hospital would require one or more authentication/authorization servers that would need to be configured to verify who is granted access to the network and what they are allowed to access. Even if a vendor and hospital purchase a turnkey VPN solution from one of the major VPN vendors, such as Cisco or Nortel, there is still significant configuration needed to establish the connection on both sides. Often there is not enough expertise on one side or the other to get this to work. The problem may be compounded by using different vendor solutions on either side of the connection that do not easily communicate with one another, since there is no universal standard for implementing VPNs today. As a result, even if a hospital IT department offers VPN connectivity and a medical device vendor says it can support a VPN connection, they may not be able to get the connection established. Or it may take substantial time to implement the connection.
VPN Policies
Most IT departments, both in hospitals and at vendors, have policies regarding VPN connectivity. It would benefit a biomed department to have an understanding of its hospital’s policy and capabilities, and then make sure that discussions take place during the selection process to ensure that remote connectivity is not only offered, but can be implemented. Again, during the selection process, biomeds should make sure that a vendor clearly specifies what service can be provided remotely, what is required of the hospital in terms of offering a connection, and any costs associated with setup and ongoing use of remote support. Once a vendor has been selected, the biomed department should determine who at the vendor site will need access and ensure that all the necessary paperwork required by IT to grant access has been completed.
Finally, there are a few other issues to keep in mind with VPN connectivity. With the move to allow more remote support, HIPAA security requirements, etc, some device vendors are now implementing very strict security on their devices. For example, they may set up individual firewalls on their devices that only allow access to certain vendors’ resources. While this is certainly beneficial in protecting a device successfully, it may also make it much more difficult to troubleshoot a device. For instance, some devices are now so tightly restricted that they will not even support a simple ping test to determine if they are connected to the network. As a result, it becomes difficult to determine if the problem exists with a device or the network infrastructure connected to the device. This requires more support from vendors than in the past, and if this is billed on a time-and-materials basis, a hospital may be spending additional money having a vendor rule out something that a biomed or hospital IT staffer could have done in the past.
Once a VPN is established for a single device or group of devices, every new device added to the network that a vendor needs to access must be set up on both sides of the VPN. This is often overlooked as new devices are installed. Then, when remote support is needed, it is not available because access to that device has not been granted on one or both sides of the VPN. As a result, biomeds should make sure that VPN connectivity is established for every new device installed and have the vendor test remote connectivity as part of the on-site acceptance testing.
Remote support is a necessary tool for the successful support of today’s medical equipment, but biomeds should keep in mind that there are many challenges involved with setting up remote connectivity. By remaining in touch with the hospital’s IT staff and policies governing remote access, biomeds can serve as valuable liaisons for the hospital in establishing this needed level of support.
Ken Olbrish, MSBE, is an enterprise imaging system administrator in the Information Services Department for the Main Line Health System, suburban Philadelphia. For more information, contact .



