By Jeff Kabachinski, MS-T, BS-ETE, MCNE
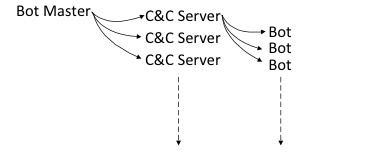
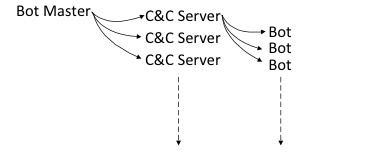 The bot master chain of command, via command-and-control servers.In part 1 of this two-article series, we explored the basics of Internet domain names and associated connectivity processes. In this installment, we will take a look at how cyber criminals use the domain concepts covered in part 1 to generate new domains to connect their command-and-control (C&C) channels with an army of bots to carry out their work.
The bot master chain of command, via command-and-control servers.In part 1 of this two-article series, we explored the basics of Internet domain names and associated connectivity processes. In this installment, we will take a look at how cyber criminals use the domain concepts covered in part 1 to generate new domains to connect their command-and-control (C&C) channels with an army of bots to carry out their work.
Security is always an issue in healthcare IT, and it’s important to be aware of the latest threats. Therefore, the focus of this article will be on the growing trend of domain-generation algorithms (DGAs). These represent a special sort of problem in terms of exploit timing and keeping an eye out for bogus domains used by your computer for communicating.1
How DGAs Work
A DGA is a type of algorithm that generates a large number of domain names so that a few can be used to open up C&C channels to give bots their assignments. As Gunter Ollmann, vice president of research for Damballa, puts it, “While DGAs are not new, the rate at which they are being adopted and their ability to elude the scrutiny of some of the most advanced malware analysis professionals should be of great concern to incident response professionals.”2
A computer is recruited into a botnet by a number of means. Maybe you were tricked into downloading a Trojan via an email message. Or maybe you fell prey to a “drive-by download,” whereby clicking on an advertisement to open a white paper you also unknowingly downloaded bot malware. Or maybe you fell victim to a web-browser vulnerability where the browser security settings can be changed, allowing other software modules to enter and plant themselves in your machine.
Bots and botnets are remote controlled by their C&C servers. They get commands to send spam, steal private information, host phishing web pages, and take part in a distributed denial of service operation (DDoS). A DDoS occurs when many bots submit requests to a particular website or computer on the Internet, thereby overloading it and making it unavailable for legitimate requests.3
Bots must have a way to surreptitiously connect to a C&C master for remote control and to receive instructions. They also need to be instructed as to where to pass any stolen data. When some other hacker (legal or illegal) intercepts the stolen data on its way back from the bot, it’s called sinkholing.4 If they’re illegal, they may sell it back to you and promise to shut down the overall attack. Or they may just use any stolen data for their own purposes. If legal, they may inform the attacked entity, protect the intercepted data, and shut down the connection.
The DGA idea started when the bot malware would be given a static list of domains to use to find a C&C server. By cycling through the list, the bot would find a live connection and “report for duty.” The longer the list of possible C&C domains, the more difficult it is to discover them. Once found out, the bogus domain gets added to the blacklist maintained at the domain servers.
However, these centralized C&C servers become a single point of failure for such an operation. To get around that, why not generate a lot more domain names? To overcome the weakness of hard-coded static lists being discovered, the newer kind of configuration files get updated routinely—in many cases, on a daily basis. The DGA, by using the date and time of operation (of running the algorithm) and another possible seed value, will generate a new list of possible open C&C channels and begin searching it to find a C&C server that’s up and listening—also known as a live connection. With the typical 1% hit rate, a list of 50,000 possible domains can generate 500 different live connections.
Fast Fluxing
An Internet entity is known by its IP address. The IP address contains the network and node IDs to identify its location. A fully qualified domain name (FQDN) does the same thing, but by using the full URL (uniform resource locator). As mentioned in part 1, the FQDN is read backward to find a specific node on the Internet, as it must also contain the network and node ID. An FQDN gets resolved to its associated IP address by the routers and devices that control network traffic. Cyber criminals often use fast fluxing or domain fluxing to quickly change what IP address gets resolved. It could also mean that it can get resolved to a number of different IP addresses, since they don’t care exactly which C&C server in the botnet is used to carry out instructions.5
Bot Herders and Your Servers
Servers are not immune. You may think that servers are well maintained, closely watched, and do not carry the typical MS Office type of data. Think again. It’s surprising how many servers double as workstations and therefore have the kinds of end user data and interactive software exposures that cyber criminals look for. This kind of end user and interactive software directly processes content from the Internet. This activity exposes the targeted software to malformed data or buffer overflow and other vulnerabilities that more generic workstations face, but with a much greater impact.6
Recap
Several concepts of DGAs go hand-in-hand to foil network authorities and law enforcement:
- They create a nimble C&C dynamic domain that only runs for short periods of time, making it difficult to find and be shut down. The C&C domain typically shuts itself down just 24 hours after registration.
- They also use a just-in-time approach to domain name server registration for short configuration timing, such as registering the domain just an hour or so before use.
- Combined, these tactics make it difficult for domain blacklists and other filtering systems based on static reputation to develop a list of C&C domains or botmaster communication channels.7
To defend against such threats, be sure to use all the typical self-protection techniques available—they go a long way to maintain security. These are the often-heard techniques such as keeping up with software updates and patches, keeping your virus scanners up to date, having firewalls in place, and not opening email from suspect or unknown sources. 24×7
Jeff Kabachinski is the director of technical development for Aramark Healthcare Technologies in Charlotte, NC. For more information, contact [email protected].
References
1. Botnets. Available at: http://en.wikipedia.org/wiki/Botnet. Accessed November 2, 2013.
2. Brenner B. (February 28, 2012). #RSAC: Domain generation algorithm tricks used by 6 crimeware families to carry out attacks. Available at: http://blogs.csoonline.com/print/2045. Accessed October 31, 2013.
3. Newton H. (2013). Newton’s Telecom Dictionary: Telecommunications, Networking, Information Technologies, The Internet, Wired, Wireless, Satellites and Fiber. 27th ed. New York City: Flatiron Publishing; 2013.
4. Ollman G. (October 24, 2011). Sinkholing for profit. Available at: http://www.darkreading.com/hacked-off/sinkholing-for-profit/231901528. Accessed November 2, 2013.
5. Antonakakis M, Perdisci R, Nadji Y, et al. From throw-away traffic to bots: Detecting the rise of DGA-based malware. Available at: https://www.usenix.org/system/files/conference/usenixsecurity12/sec12-final127.pdf. Accessed November 11, 2013.
6. Smith RF. (2012). Keeping bot herders off your servers and breaking the lateral kill chain of today’s attackers. Available at: https://www.lumension.com/Media_Files/Documents/Marketing—Sales/Whitepapers/Keeping-Bot-Herders-Off-Your-Servers.aspx. Accessed November 11, 2013.
7. Dambella Inc. (2012). DGAs in the Hands of Cyber-Criminals: Examining the state of the art in malware evasion techniques. Available at: http://www.metadigm.co.uk/partners/resources/downloads/Damballa_DGAs_in_the_Hands_of_Cyber_Criminals.php. [registration required]. Accessed November 11, 2013.