By Arleen Thukral, MS
Wireless devices, which are increasingly prevalent in hospitals, offer numerous benefits. For starters, the convenience of being able to bring the medical device to any facility location can boost productivity. And then there’s the fact that portability allows for a quick workflow and cost-effective setup.
The economies of scale provide another advantage as additional clients (i.e., infusion pumps or vital sign machines) can be deployed without additional wiring, unlike in a wired network. Because more medical device data is being transmitted wirelessly, it’s imperative that biomedical equipment specialists and biomedical engineers are well acquainted with wireless technology.
Wireless networks can operate in one of two basic modes: infrastructure and ad-hoc. In infrastructure mode, clients connect to an access point; no access point is involved in ad-hoc mode, however. Instead, clients communicate with each other.
Wireless Technology Standards
“802.11” is the Institute of Electrical and Electronic Engineers’ (IEEE’s) term for the working group of wireless local area networks. (The IEEE identifies each standard with a letter, with 802.11a differing from 802.11b, for instance.) Although some commonalities exist between technologies, key differences include speed, modulation techniques, and backward compatibility. For instance, even though 802.11g was developed after 802.11b, it still supports Wired Equivalent Privacy to ensure backward compatibility.
| Standard | Frequency | Speeds | Interoperates with |
| 802.11a | 5 GHz | 54 Mbps | None |
| 802.11b | 2.4 GHz | 11 Mbps | None |
| 802.11g | 2.4 GHz | 54 Mbps | 802.11b |
| 802.11n | 2.4 GHz/5 GHz | 100 Mbps and higher | 802.11b, 802.11g |
Access Points
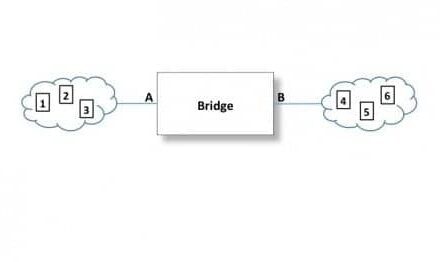
Access points (APs) are a vital component of a scalable wireless network, with AP hardware consisting of radio transceivers, antennas, and device firmware. A physical device, AP hardware acts as a liaison between wireless and wired communications.
Lately, you can configure an access point from a web interface or a full-fledged command line. For large-scale deployments, a management system is installed on a server to allow administrators to automate the configuration of APs with a template profile that has a specified service set identifier (SSID), encryption and authentication method. Note: This would still require the administrator to configure basic Internet Protocol connectivity on the access point and enable Telnet.
Essential Unique Identifiers
The SSID, along with the basic service set identifier (BSSID), and media access control (MAC) address are all essential unique identifiers for a wireless network. The SSID is the wireless “network name” and can be shared by multiple access points. The BSSID, on the other hand, uniquely identifies a specific access point and appears in the same format as a MAC address.
Access points send out beacons, which are radio broadcasts that advertise the wireless settings containing the SSID, encryption method, etc. As you might expect, the closer a user is to an access point, the stronger the signal and the faster the connection speed. In order to connect to an access point and join a wireless network, medical devices must be equipped with a wireless network adapter. These are often built as add-on adapters plugged into an empty expansion slot, a USB port or a personal computer card slot.
When designing AP placement in a hospital, it’s important to consider the number of clients. For instance, modern access points support up to 255 clients. Further, a wireless spectrum analyzer can be utilized to ensure Wi-Fi coverage on each floor.
Wireless Interference
Remember: The potential for interference is great indoors, where different types of building materials (i.e., concrete, wood, drywall, metal, glass, etc.) can absorb or reflect radio waves, affecting the strength and consistency of a wireless network’s signal.
Devices that operate in the same 2.4 frequency range as 802.11 networks also cause interference, such as microwaves and radios. Strategies to minimize interference include relocating wireless networking hardware, using specialized antennas, and investing in radiofrequency shielding.
Wireless Network Security
Although it’s impossible to hide the presence of a network from strangers, you can prevent unauthorized access and protect data. Fortunately, wireless encryption has undergone numerous iterations to keep ahead of hackers. Different techniques may be more appropriate for different applications; for instance, shared-key schemes are fast and require less computing power while public key schemes are extremely secure.
Further, Wired Equivalent Privacy (WEP) is the oldest and least secure method and should be avoided. With WEP, all devices on a wireless network must use the same kind of encryption and be configured with the same password.
Wi-Fi Protected Access (WPA), on the other hand, was developed to replace WEP—with WPA-Personal using a key that is 256 bits long. Compared to WPA-Personal, WPA-Enterprise is more complicated to configure since it requires additional servers to perform authentication of each individual user (Remote Authentication Dial-In User Service client/server protocol and software). Even so, it’s easier to maintain, as unique authentication credentials can be disabled without affecting all systems.
Finally, WPA2 supports the Temporal Key Integrity Protocol encryption algorithm and is referred to as “AES”. The AES—aka, Advanced Encryption Standard—has been around for many years and remains relevant today. Whenever possible, you should configure your access points and clients to use WPA2.
Arleen Thukral, MS, is chief biomedical engineer at VA Central California Health Care System in Fresno.