The Health Sector Coordinating Council’s (HSCC) Cybersecurity Working Group (CWG) published the “Operational Continuity-Cyber Incident (OCCI)” checklist for addressing cyberattacks.
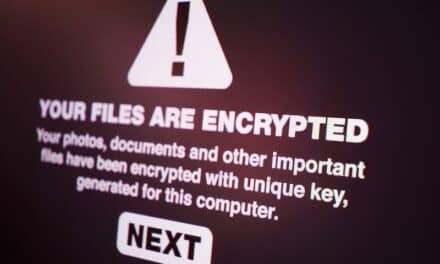
This HSCC toolkit is intended to provide a flexible template for operational staff and executive management of healthcare organizations to respond to and recover from an extended enterprise outage due to a serious cyberattack. The checklist’s operational structures and tasks can be modified or refined according to an organization’s size, resources, complexity, and capabilities.
the checklist aims to represent collective thinking of health sector cybersecurity and emergency management executives contributing to the HSCC Incident Response/Business Continuity (IRBC) Task Group. It is not associated in with any regulatory compliance program, the HSCC says.
The HSCC serves as an official advisory council to its government counterparts—HHS and FDA—with a formally-designated critical infrastructure protection function distinct from the advocacy and member services roles of traditional industry associations.
In late April, the Cybersecurity and Infrastructure Security Agency (CISA) once again sounded the alarm on Russian state-sponsored cyber threats. CISA urged critical infrastructure to patch all systems, secure Remote Desktop Protocol (RDP), and implement multifactor authentication.
Even without a direct cyberattack against US healthcare organizations, the American Hospital Association (AHA) suggested that the sector could become collateral damage to Russian-deployed malware.
With geopolitical tensions in mind, HSCC’s guide tackles the possibility of a “prolonged massive disruption,” which it defined as an incident that potentially impacts patient safety and clinical workflows.
Read the full article at Health IT Security.