The U.S. FDA is alerting equipment users and manufacturers about medical device vulnerabilities for the Axeda agent and Axeda Desktop Serve, which were detected by Forescout’s Vedere Labs, in partnership with CyberMDX.
Moreover, the Cybersecurity and Infrastructure Security Agency (CISA) rated three of the seven medical device vulnerabilities as “critical” as they could enable hackers to remotely execute malicious code and take full control of devices, access sensitive data, or alter device configurations. On the heels of this development, Elad Luz, head of research at CyberMDX, sat down with 24×7 Magazine to discuss the implications of this news and why medical device cybersecurity is more critical than ever.
24×7 Magazine: Can you please discuss in greater detail the vulnerabilities Vedere Labs disclosed?
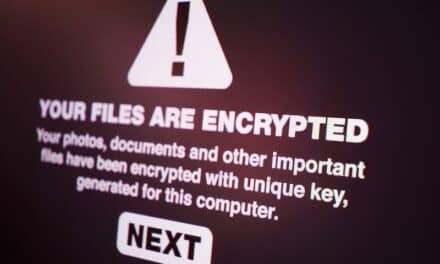
Elad Luz: On Tuesday, March 8, Vedere Labs and CyberMDX disclosed Access:7, a set of seven vulnerabilities that affect a software agent called Axeda, which is owned by PTC. Device manufacturers and software companies use Axeda to remotely manage, service, and maintain devices installed by customers.
Exploiting these vulnerabilities could result in remote code execution, read access to the device file system, and deny service for the agent software. We estimate that it affects more than 100 different device models and 150-plus manufacturers.
24×7: Why are these medical device vulnerabilities so critical from a patient safety perspective?
Luz: One hundred different vendors use or have used Axeda in the past, most of them coming from the healthcare industry. The agent is used on critical patient equipment, as well as imaging and lab devices. Given that affected devices could be compromised, remote code execution might lead to misdiagnosis, false treatment, and delay in patient care. In addition, connected medical devices carry sensitive information, so information-leak could be an issue.
24×7: What are your reactions to CISA’s advisory regarding the PTC Adexa agent and the Adexa Desktop Server?
Luz: CISA’s advisory is a result of the responsible disclosure process we are undergoing with them—and a critical part of this project with CISA, PTC, Vedere Labs, and CyberMDX. The advisory contains a brief description of each vulnerability, mitigations, and links to advisories by several vendors. The bundle of vulnerabilities received a CVSS score of 9.8 out of 10.0, which means these issues are critical.
24×7: Do you think the medical device industry is adequately concerned about cybersecurity?
Luz: Both medical device manufacturers (MDMs) and health delivery organizations (HDOs) are working hard to close the gaps, but the situation is challenging. Medical devices have a relatively long lifespan, which usually leaves them with deprecated software. New software versions take more time to develop, as they require extensive testing and regulation approval. Patches and updates are slowly deployed, as this usually only happens within a limited maintenance timeframe and might require boots on the ground. The healthcare industry requires a unique solution for these challenges, and we are pleased to be able to offer a solution to help mitigate these issues.
24×7: As an executive at CyberMDX, what do you want to tell HTM professionals about medical device cybersecurity, in general?
Luz: One of the reasons vulnerabilities are disclosed publicly is for raising awareness. We hope the findings of our research motivate both MDMs and HDOs to check how their own remote vendor support and services are implemented and perform a risk assessment so they can protect their networks.