To help healthcare IT leaders better understand zero-trust principles and examine vendor architectures, the global IT research and advisory firm Info-Tech Research Group published a new industry blueprint, Navigate Zero-Trust Security in Healthcare.
How Does the Zero-Trust Model Work?
Zero-trust architecture has gained paramount importance as the healthcare industry starts to include more connected Internet of Medical Things (IoMT) devices, augmented reality, and robotics within care pathways.
However, the zero-trust model—never trust, always verify, assume breach, and verify explicitly—is not a one-size-fits-all approach. The road to zero-trust is an iterative process that relies on the IT security team to be thoughtful in determining how moving to a zero-trust model will affect core processes and patient care.
Further reading: Best Practices for Thwarting Medical Device Cyberattacks
A fully implemented zero-trust solution makes it harder for attackers to access, encrypt, or steal digital assets such as medical health records. Zero-trust helps healthcare IT security teams manage risk across multiple domains, including devices, applications such as billing and scheduling, identities, and data.
While healthcare CIOs and CISOs recognize the value of pursuing a zero-trust security strategy, they can also encounter several challenges including:
- Winning over a skeptical clinical audience in applying the principles of zero-trust.
- Difficulties in the ability to identify, track, and verify all devices in their healthcare network.
- Moving away from a perimeter-based security architecture to a zero-trust architecture while demonstrating that this change will support the provision of healthcare.
Zero-trust is a strategy that forgoes reliance on perimeter security and moves controls to where users access resources. It consolidates security solutions and saves operating expenditures while also enabling business mobility by securing the digital environment at all layers.
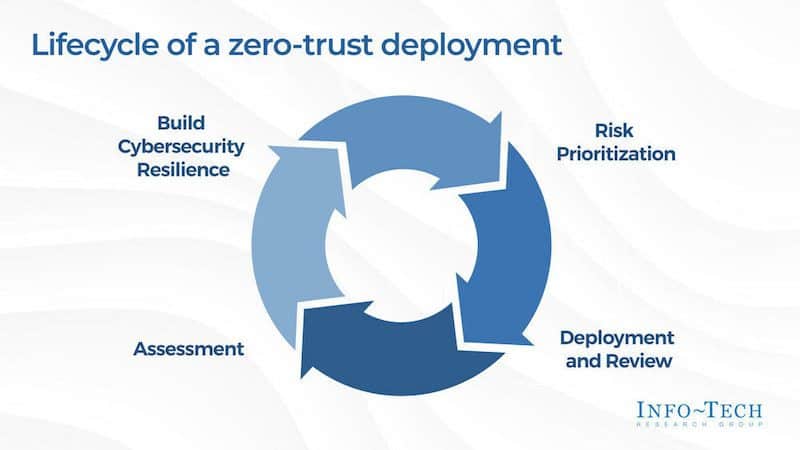
Knowing where to start is crucial for IT leaders, as zero-trust is not only complex from an architectural perspective, but there is also no clear checklist to follow when revising your security posture to adopt zero-trust. The blueprint suggests to leaders and their teams the following lifecycle of a zero-trust deployment:
- Build cybersecurity resilience
- Risk prioritization
- Deployment and review
- Assessment
As well, Info-Tech advises the following steps when implementing a zero-trust architecture, especially in a healthcare environment, according to Info-Tech Research Group:
- Define objectives before architecting a zero-trust environment.
- Design from the inside out rather than from the outside in.
- Plan to achieve a centrally managed platform rather than distinct, multiple tools.
As examples and additional guidelines, the blueprint also recommends examining the security architectural frameworks that organizations like Microsoft and Google have applied to their environments.
To modernize and safeguard the technology assets of healthcare organizations, Info-Tech advises that IT must convince clinical leaders to add more security controls that go against the grain of reducing friction in workflows while demonstrating these controls support the organization. When implemented properly, zero-trust embeds security into existing processes.
To learn more, download the Navigate Zero-Trust Security in Healthcare blueprint.
Featured image: The guide for zero-trust deployment in the healthcare industry from Info-Tech Research Group’s “Navigate Zero-Trust Security in Healthcare” blueprint. Graphic: CNW Group/Info-Tech Research Group