A side-by-side look at platforms used by HTM teams to identify connected devices, prioritize risk, and manage cybersecurity across hospital environments.
This guide compares cybersecurity platforms used by healthcare technology management (HTM) teams to identify connected medical devices, assess risk, and support mitigation across hospital environments. It breaks down key capabilities—including asset discovery, risk scoring, vulnerability management, and workflow integration—to help teams evaluate which platforms align with their operational needs.
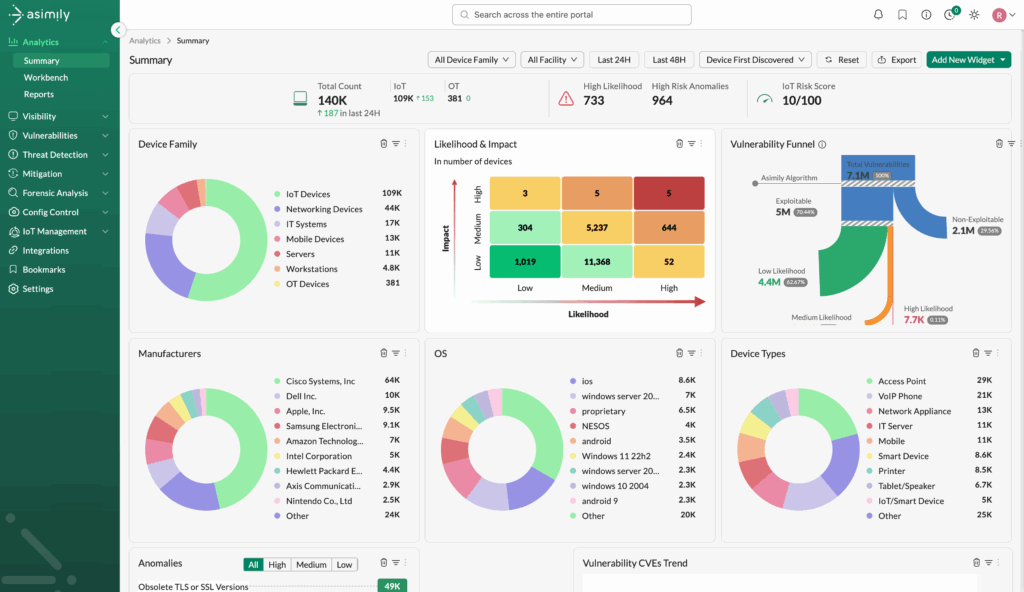
Asimily – Asimily
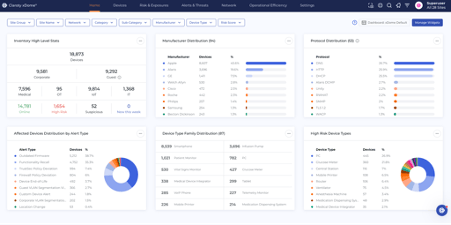
Claroty – Claroty xDome
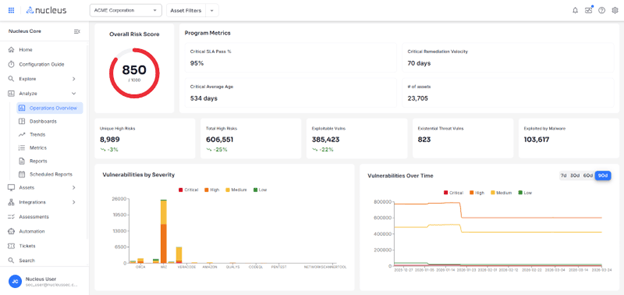
Nucleus Security – Nucleus Security Platform
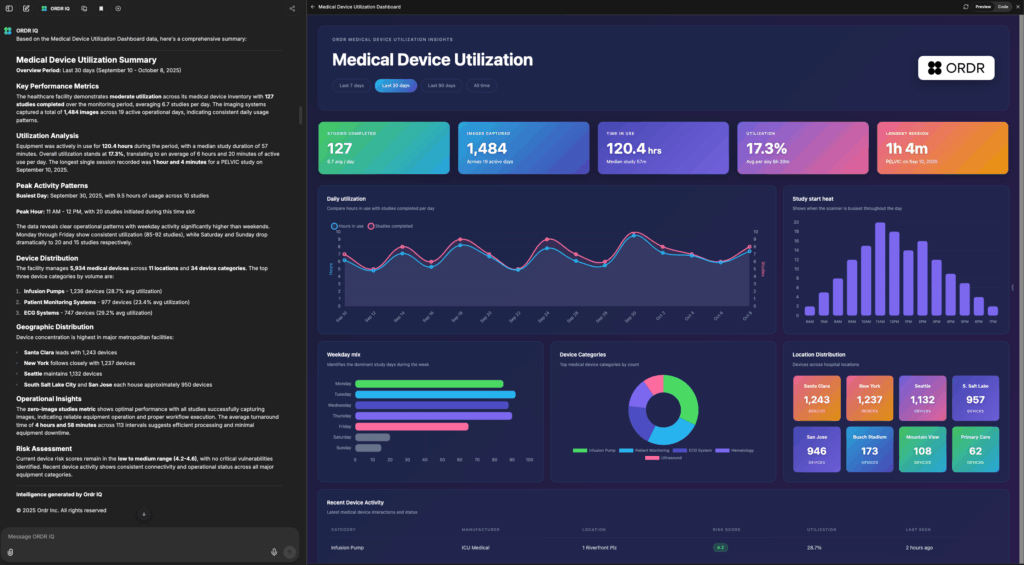
ORDR – ORDR AI Protect Platform
| Company Name: | Asimily | Claroty | Nucleus Security | ORDR |
|---|---|---|---|---|
| Cybersecurity software: | Asimily | Claroty xDome | Nucleus Security Platform | ORDR AI Protect Platform |
| Website: | asimily.com | claroty.com/healthcare-cybersecurity/xdome-for-healthcare | nucleussec.com | ordr.net |
| Description: | Asimily reduces risk present on the riskiest 1% of cyber assets by identifying, prioritizing, and mitigating dangers. We drive revenue and cut capital expenditures by boosting uptime by providing insights and defense for critical cyber assets. | Claroty xDome is a purpose-built cyber-physical systems (CPS) platform that provides tailored device visibility and actionable insights across exposure management, threat detection, and network protection, enabling increased risk resilience and operational continuity through unified management of connected clinical systems. | Nucleus Security delivers a platform that unifies vulnerability data across tools, enriches it with real-world exploitation intelligence, and enables healthcare organizations to prioritize risk, prevent breaches, and accelerate secure, automated remediation workflows across clinical and IT environments. | ORDR is the only purpose-built platform to help organizations see, know, and secure every connected device—from traditional servers and workstations to IoT, IoMT, and OT devices. Crunchbase competitors often specialize in one segment; ORDR provides a unified view across all device types. |
| Last Major Update: | March 2026 | 2025 | 2025 | March 2026 |
| Introduced in the Last Software Update: | Network Topology View provides a graphical, comprehensive map detailing the flows of network traffic, all with Asimily’s calculated risk posture. | Introduced context-aware Exposure Scenarios for risk prioritization, peer-informed Risk Benchmarking, and MITRE-mapped Advanced Threat Detection. | AI-driven exposure management with unified data, custom risk scoring, and automated workflows to reduce healthcare cyber risk faster. | ORDR IQ, multi-agent AI orchestrator for end-to-end workflows, exposure risk to highlight risk based on compliance requirements |
| Asset Discovery Method: | Passive network monitoring, active querying, agent-based discovery, integration with existing IT systems, cloud-based visibility | Passive network monitoring, active querying, integration with existing IT systems, cloud-based visibility | Integration with existing IT systems, cloud-based device visibility | Passive network monitoring, active querying, agent-based discovery, integration with existing IT systems, cloud-based visibility, log analysis |
| Level of Device Identification: | Advanced + (identifies care area) | Advanced + (identifies care area) | Intermediate (manufacturer + model) | Advanced + (identifies care area) |
| Risk Scoring Approach: | CVE-based scoring, contextual risk, patient safety/clinical impact considered, customizable risk scoring by facility, threat intelligence integration | CVE-based scoring, contextual risk, patient safety/clinical impact considered, customizable risk scoring by facility, threat intelligence integration, KEV and EPSS scores | CVE-based scoring, contextual risk, patient safety/clinical impact considered, customizable risk scoring by facility, threat intelligence integration | CVE-based scoring, contextual risk, patient safety/clinical impact considered, customizable risk scoring by facility, threat intelligence integration, connectivity, business context, exposure based on gaps/compliance |
| SBOM and Vulnerability Management: | SBOM ingestion supported, SBOM visibility at device level, maps vulnerabilities to specific devices, provides remediation/mitigation guidance, tracks patch status | SBOM ingestion supported, SBOM visibility at device level, maps vulnerabilities to specific devices, provides remediation/mitigation guidance, tracks patch status | SBOM ingestion supported, maps vulnerabilities to specific devices, provides remediation/mitigation guidance, tracks patch status | SBOM ingestion supported, SBOM visibility at device level, maps vulnerabilities to specific devices, provides remediation/mitigation guidance, tracks patch status |
| Network Visibiliy and Segmentation Support: | Real-time network traffic monitoring, device communication mapping, segmentation policy recommendations, integration with NAC/firewalls, microsegmentation support | Real-time network traffic monitoring, device communication mapping, segmentation policy recommendations, integration with NAC/firewalls, microsegmentation support | Integration with NAC/firewalls | Real-time network traffic monitoring, device communication mapping, segmentation policy recommendations, integration with NAC/firewalls, microsegmentation support |
| Integration Capabilities: | CMMS integration, ITSM/ticketing system integration, SIEM/SOC integration, API available for custom integrations | CMMS integration, ITSM/ticketing system integration, SIEM/SOC integration, API available for custom integrations | ITSM/ticketing system integration, SIEM/SOC integration, API available for custom integrations | CMMS integration, ITSM/ticketing system integration, SIEM/SOC integration, API available for custom integrations |
| Alerting and Workflow Features: | Risk-based alert prioritization, customizable alert thresholds, role-based dashboards, automated ticket generation, alert suppression/noise reduction features | Risk-based alert prioritization, customizable alert thresholds, role-based dashboards, automated ticket generation, alert suppression/noise reduction features | Risk-based alert prioritization, customizable alert thresholds, role-based dashboards, automated ticket generation, alert suppression/noise reduction features | Risk-based alert prioritization, customizable alert thresholds, role-based dashboards, automated ticket generation, alert suppression/noise reduction features |
| Deployment Model: | Hybrid | SaaS (cloud-hosted) | SaaS (cloud-hosted) | SaaS (cloud-hosted) |
| Typical Deployment Time: | <30 days | <30 days | 1-3 months | <30 days |
| Support for Legacy/Unsupported Devices: | Visibility into legacy operating systems, monitoring without installing agents, compensating control recommendations, risk scoring adjusted for unsupported devices, supports devices that cannot be patched or updated | Visibility into legacy operating systems, monitoring without installing agents, compensating control recommendations, risk scoring adjusted for unsupported devices, supports devices that cannot be patched or updated | Visibility into legacy operating systems, monitoring without installing agents, compensating control recommendations, risk scoring adjusted for unsupported devices, supports devices that cannot be patched or updated | Visibility into legacy operating systems, monitoring without installing agents, compensating control recommendations, risk scoring adjusted for unsupported devices, supports devices that cannot be patched or updated |
| Reporting and Compliance Support: | Prebuilt risk reports, custom report builder, executive-level dashboards, compliance reporting, audit/survey support documentation, reports aligned to Joint Commission/audit needs | Prebuilt risk reports, custom report builder, executive-level dashboards, compliance reporting, audit/survey support documentation, reports aligned to Joint Commission/audit needs | Prebuilt risk reports, custom report builder, executive-level dashboards, compliance reporting | Prebuilt risk reports, custom report builder, executive-level dashboards, compliance reporting, audit/survey support documentation, reports aligned to Joint Commission/audit needs |
| Clinical/HTM Workflow Support: | Supports biomed/HTM-specific workflows, provides device service history or utilization reports, enables collaboration between HTM and IT teams, generates work orders or service tickets | Supports biomed/HTM-specific workflows, provides device service history or utilization reports, enables collaboration between HTM and IT teams, generates work orders or service tickets | Generates work orders or service tickets | Supports biomed/HTM-specific workflows, provides device service history or utilization reports, enables collaboration between HTM and IT teams, generates work orders or service tickets |
| Pricing Model: | Annual subscription, per-bed pricing, tiered pricing | Annual subscription, per-device pricing, enterprise flat-rate pricing, tiered pricing | Annual subscription, per-device pricing, tiered pricing | Annual subscription, per-device pricing, per-bed pricing, tiered pricing, per employee |
| Typical Annual Cost Range: | Dependent on unique hospital | n/a | $40,000-<$1M | 300 bed; ASP $150,000 |
Last updated April 2026.
Information for this guide is based on data submitted by cybersecurity software marketers. 24×7 strives for accuracy in all data but cannot be held responsible for claims made by marketers. All cybersecurity software marketers get one listing at no charge. Advertisers are offered multiple listings. All cybersecurity software platforms may not be included. Email [email protected] to be considered for the next update.