By Rob Suárez
There is one major difference between cybersecurity in healthcare and cybersecurity in other industries, such as finance or retail. In healthcare, human lives are at stake. We know that software-enabled medical technologies are critically important to improving patient outcomes and the quality of care. However, we also know that all software develops vulnerabilities over time, and medical devices are no exception.
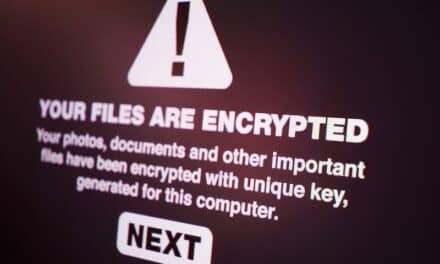
Software vulnerabilities can impact device functionality and data privacy. They can also be an attack vector for ransomware, which has become a growing concern across the industry. In 2020, one in three healthcare organizations around the world received ransomware. Since then, ransomware attacks in healthcare have increased, with more than 100 documented attempts per week across the industry in the first half of 2021.
With the expectation that the pace of cyberattacks in healthcare will continue into 2022, it is crucial for healthcare providers to manage cybersecurity risks effectively. This requires understanding potential cybersecurity risks and how to manage them not only in the short term, but over the intended lifecycle of each medical device. The following strategies can help healthcare providers and medical device manufacturers work together to manage medical device cybersecurity amid increasing cyber-risks:
Communicate About Medical Device Cybersecurity Risks
To protect medical devices from cyberattacks, healthcare delivery organizations must know the risks associated with each device. That’s where ongoing communication between medical device manufacturers and healthcare delivery organizations is critical. This topic is so important, in fact, the U.S. FDA Center for Devices and Radiological Health (CDRH) issued Best Practices for Communicating Cybersecurity Vulnerabilities to Patients in October 2021. While the document does not represent formal guidance, it illustrates the criticality of transparency and collaboration between medical device manufacturers and healthcare delivery organizations.
In short, healthcare providers cannot protect against vulnerabilities they do not know about. It’s not enough for manufacturers to identify potential risks. We must also commit to communicating about vulnerabilities in a timely manner, using plain language and channels that are easily accessible. At BD, for instance, vulnerability disclosures are posted to the BD Cybersecurity Trust Center website. We also voluntarily report vulnerabilities to the FDA and Information Sharing Analysis Organizations where BD participates, including the U.S. Department of Homeland Security Cybersecurity & Infrastructure Security Agency and the Health Information Sharing and Analysis Center for maximum awareness.
Making information about cybersecurity risks and vulnerabilities easily accessible enables healthcare delivery organizations to access the information they need to protect patient safety and privacy.
Communicate About Third-Party Software Components
As an industry, we are moving toward including a more detailed software-bill-of-materials to increase transparency around third-party software components. Having this information gives healthcare providers more complete visibility regarding the software components that could impact their networks. This allows customers to respond more quickly when zero-day vulnerabilities and other risks are identified in third-party software components that are widely used in medical devices. Transparency also equips healthcare providers with the information they need to prioritize patch management for the most vulnerable devices or systems.
Plan for Devices to Go End-of-Life
Hospital networks operate as many as 350,000 medical devices at a time. Each of those devices may be useful for up to 15 years. However, the lifecycle of third-party software components—including operating systems—is usually much shorter, even with extended support options.
Medical devices must be designed and developed with cybersecurity in mind. However, no technology is 100% secure. When technology goes end-of-life, it also reaches the end of security updates. This means that vulnerabilities go unpatched, making them particularly vulnerable to cyberattacks. That’s why it’s so important for medical device manufacturers and healthcare delivery organizations to make planning for end-of-life part of the procurement process. This means planning for procurement cycles, including implementation costs and upgrades, while securely decommissioning legacy devices over time.
In healthcare cybersecurity, protecting patient safety and privacy is our highest priority. Every step we take to improve collaboration between medical device manufacturers and healthcare providers—including communicating about cybersecurity risks, third-party software components, and medical device lifecycles—helps to advance cybersecurity in healthcare and protect patient safety and privacy.
Rob Suárez, HCISPP, is vice president and chief information security officer for BD (Becton, Dickinson and Company).
References:
- Kelley D. Top 3 ransomware attack vectors and how to avoid them. TechTarget. https://searchsecurity.techtarget.com/tip/Top-3-ransomware-attack-vectors-and-how-to-avoid-them. Published September 2021. Accessed Oct. 4, 2021.
- Pifer R. More than 1/3 of health organizations hit by ransomware last year, report finds. Healthcare Dive. https://www.healthcaredive.com/news/more-than-13-of-health-organizations-hit-by-ransomware-last-year-report-f/602329/. Published June 24, 2021. Accessed Sept. 22, 2021.
- Davis J. Ransomware Keeps Healthcare in Crosshairs, Triple Extortion Emerges. Health IT Security. https://healthitsecurity.com/news/ransomware-attacks-surge-102-in-2021-as-triple-extortion-emerges. Published May 14, 2021. Accessed Sept. 24, 2021.
- Bracken B. Ransomware’s New Swindle: Triple Extortion. Threatpost. https://threatpost.com/ransomwares-swindle-triple-extortion/166149/. Published May 14, 2021. Accessed Aug. 17, 2021. Accessed Sept. 24, 2021.
- Rozumalski K. Working together to secure our expanding connected health future. Help Net Security. https://www.helpnetsecurity.com/2020/10/06/working-together-to-secure-our-expanding-connected-health-future/. Published Oct. 6, 2020. Accessed Aug.17, 2021.