As HTM departments scramble to address the “Bash bug,” cybersecurity experts warn there’s much more to come
The news, Chris Peters recalls, arrived in an advisory from the University of Michigan’s Information and Infrastructure Assurance (IIA) division. “A security vulnerability was announced today that requires immediate remediation,” the notice, from September 24, began. “Please read…to see if servers for which you are responsible are affected and take action if appropriate.”
Peters, a clinical engineer in the biomedical engineering department at UM Hospitals and Health Systems, did as he was asked. “A vulnerability in Bash,” the notice continued, “could allow an attacker to execute arbitrary commands on a server, which could result in exposure of sensitive information or negative impact to critical services…. Any service running on a system with a vulnerable version of Bash may be susceptible to attack.” And then, ominously, “widespread exploitation is expected to occur quickly.”
The advisory, explaining that affected systems included anything running on Linux, Apple, or other Unix-based operating systems, recommended applying vendor patches to those systems as soon as possible, but also noted that, “IIA will not be scanning campus networks to identify vulnerable systems because a reliable method for remotely detecting” such systems was not available.
This, Peters remembers thinking, was a problem. “I mean, you look around, and there is equipment everywhere that may or may not be vulnerable—physiological monitors, ultrasound machines, tablet computers” being used to interface with medical equipment through the wireless network. “The big question for me was, and still is, What equipment does this affect? Is it just a few devices? Or is it a lot more than we might think? And if there is an attack, what could it do to our network?”
A “Nasty” Bug
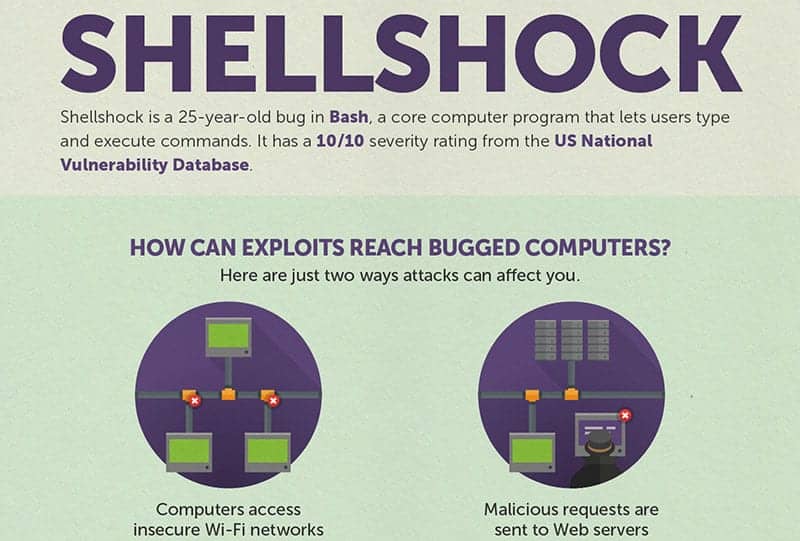
Chances are, like Peters, you’ve already been briefed on the “Shellshock” bug. First made public in an alert by the Department of Homeland Security’s US Computer Emergency Readiness Team (US-CERT), Shellshock, or the “Bash Bug,” is a security vulnerability in Bash, a computer program in Unix-based operating systems that allows users to enter and execute commands. Because the flaw is so easy to take advantage of, and because exploitation could, as software security company Trend Micro put it, “do significant widespread damage,” the National Institute of Standards and Technology has given the bug a 10 out of 10 rating on its vulnerability-severity scale. “It’s really very nasty,” notes Axel Wirth, a healthcare cybersecurity expert at Symantec Corp. If it’s exploited—in a healthcare environment or elsewhere—“the attacker can take full control of a system.”
Mike Ahmadi, global director of medical security at Internet security firm Codenomicon, adds that the Bash Bug is “interesting,” mainly because it’s so ubiquitous. “It really affects an enormous number of Linux systems, and Linux is very popular for a lot of applications in healthcare.” Web servers, routers, firewalls, and embedded medical devices with connections to the Internet are most vulnerable, Ahmadi says. Building systems like HVACs, elevator controls, and refrigeration units may also be affected.
Other industries that depend on Unix-based operating systems in their day-to-day affairs may simply deploy the recommended patches that were released almost immediately after the flaw was announced. In healthcare, however—and as Peters has seen at the University of Michigan—it’s not always so simple.
“There are a couple of problems,” Ahmadi says. “First, there’s no easy way to know which devices and systems are affected. The FDA tracks things like food ingredients, but they don’t track which versions of operating systems are included in the medical devices that they approve.” Certain versions of Linux have the Bash Bug, while other versions do not. And while “any good manufacturer should know which version of Linux is in their device,” Ahmadi says, because reporting is not mandated, that information may be hard to obtain.
“If you’re a device manufacturer, patching an OS is a big, big deal.” Manufacturers must test any patch extensively before issuing it to ensure it won’t cause a device to malfunction or fail, he explains. Then, once they have made a patch available, warranty limitations may prevent end users from applying that patch on their own. “The bottom line is, if it’s a medical device you’re worried about, there’s very little that you can do quickly.” (When representatives at GE Healthcare were asked how they were addressing potential Shellshock vulnerabilities in their medical devices, they referred to a written statement posted on the GE “Security and Compliance” page: “We are actively monitoring our data security systems in response to [the Bash Bug], and are taking swift action where necessary.”)
Action Steps
If your department already practices good inventory management, remediation may be a relatively straightforward process. As Wirth points out, “any asset-management system should include information on the operating-system versions used in the devices on your network, and that should allow you to look up, typically on the support website of the vendor, whether that version is affected, whether it should be patched, or whether they recommend other security measures.” And if you can’t find that information online? “Then you should pick up the phone and call the vendor.”
Most noncritical systems (what Wirth describes as “standard IT components”), like web servers, print servers, and internal routers and firewalls that aren’t used directly in patient care, are typically easy to patch and don’t require close vendor oversight. Patch these systems immediately, Wirth says. Devices that cannot be patched easily, on the other hand, should be safe—at least temporarily—behind the standard protections provided by your facility’s network-security architecture. Best practices, Wirth notes, include the use of firewalls and “segmenting off [vulnerable devices] in protected VLAN networks.” And traffic monitoring is key. “If a device is attacked, you want to know about it.” (The Symantec blog post, “How to Prevent Your Data from Getting Shellshocked,” lists more intrusion-prevention strategies; and a list of Linux vendors that have issued security advisories is here.)
Unfortunately, Wirth says, Shellshock will likely be remembered as just one bug on a long list of high-profile flaws “fundamentally inherent to software infrastructure.” We’ll inevitably hear news, as we did with Heartbleed, of Bash-related system breaches and data pilfering in the months ahead. And the next vulnerability? Don’t blink, because it’s already here. “This,” Wirth predicts, “is just the beginning.”
Chris Hayhurst is a contributing writer for 24×7. For more information, contact editorial director John Bethune at [email protected].
Featured image and infographic below courtesy Trend Micro.