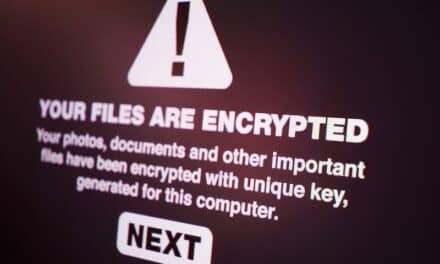
Security breaches, HIPAA violations, OCR fines—ever hear of these things? They’ve been hot topics among healthcare IT and healthcare technology management folks for quite some time. Until recently there hasn’t been much in the way of guidance or overall standards for healthcare IT. It’s mostly been security by obscurity. Well, news flash: Healthcare IT is obscure no more!
I could write several columns about all the cyber attacks and HIPAA breaches in recent years. (I think it was Benjamin Franklin who said, “There are only three things certain in life—death, taxes and cybersecurity breaches.”) Did you know that an electronic protected health information record (ePHI) can be sold for 50 times more than a valid credit card number on the black market? It’s highly lucrative to exploit healthcare IT, turning health organizations into targets. It can seem impossible for hospitals to predict where the next exploit will occur and figure out how to defend themselves. Meanwhile, the stakes associated with a breach have never been higher: Not only is losing a bunch of patient records catastrophic enough, but the Office for Civil Rights (OCR) could add insult to injury by assessing a 5- or 6-digit HIPAA breach fine to boot!
Some comfort can be taken with recent developments in the standards development arena. Over the next three issues, Networking will be presenting a series of columns to look at cybersecurity, starting with a presidential Executive Order and the resulting framework produced by the National Institute of Standards and Technology (NIST). In part 2, we’ll examine a healthcare-specific take on cybersecurity via the Health Information Trust Alliance (HITRUST) Common Security Framework. Then, in part 3, we’ll explore how HITRUST stays current in between major revisions to keep your framework up-to-date—in the hope that we in healthcare can get a timely foothold on cybersecurity!
How the Current Standards Effort Started
In 2013, President Obama issued Executive Order 13636 on “Improving Critical Infrastructure Cybersecurity” to push for better cybersecurity for American industry in general.1 The Order details all aspects of what is needed across 12 sections. Consider the following passage from the Order as an example:
Sec. 7. Baseline Framework to Reduce Cyber Risk to Critical Infrastructure. (a) The Secretary of Commerce shall direct the Director of the National Institute of Standards and Technology (the “Director”) to lead the development of a framework to reduce cyber risks to critical infrastructure (the “Cybersecurity Framework”). The Cybersecurity Framework shall include a set of standards, methodologies, procedures, and processes that align policy, business, and technological approaches to address cyber risks.
For a full listing of what the Order references, check out its complete text in the Federal Register Volume 78, Number 33.
The NIST Framework
A year later, in accordance with this directive, NIST released its own “Framework for Improving Critical Infrastructure Cybersecurity.”2 The executive summary provides a good high-level justification for this effort and why the president issued the order: “Cybersecurity threats exploit the increased complexity and connectivity of critical infrastructure systems, placing the Nation’s security, economy, and public safety and health at risk. ”
The intention of the NIST framework was to provide organizations with a cost-effective way to increase cybersecurity without adding to the various regulations and standards already in place. It was a partnered effort between the private sector and the government. The outcome allows organizations to use a template to generate their own cybersecurity framework or to cross-check their own framework and look for gaps. Organizations can then describe their current cybersecurity posture and target postures to identify and prioritize improvements. This approach allows organizations to mark their progress toward a target state and also provides a common means to communicate that state to internal and external stakeholders.
There are three general sections to the framework: the core, the implementation tiers, and the profile. The framework core is a set of cybersecurity activities, outcomes, and informative references that are common across critical infrastructure sectors, which allow organizations to develop their own individualized profiles. The implementation tiers help organizations view and understand the detailed characteristics of their approach to cybersecurity risk management. Finally, use of the cybersecurity profile allows detailed custom guidance for a particular organization by helping the organization align its cybersecurity framework with its resources, tolerance of risk, and business imperatives.
The whole idea is that an organization can make use of the NIST framework regardless of its level of cybersecurity sophistication without added regulation or standards. This should complement rather than replace any framework currently in place. In addition, as time goes on, overall lessons learned will be incorporated by NIST into the next version of the framework.
[reference float=”right”]Informative References
Below are standards and guidance cited in the NIST Framework.
CCS CSC—Council on CyberSecurity, The Critical Security Controls for Effective Cyber Defense
COBIT 5—Control Objectives for Information and Related Technology. (COBIT) is a framework created by ISACA for information technology (IT) management and IT governance. It is a supporting toolset that allows managers to bridge the gap between control requirements, technical issues, and business risks.
ISO/IEC 27001:2009 & 2013—Information technology—Security techniques—Information security management systems—Requirements specifies the requirements for establishing, implementing, maintaining, and continually improving an information security management system within the context of an organization, regardless of its type, size, or nature.
NIST SP 800-53 Rev. 4—Security and Privacy Controls for Federal Information Systems and Organizations: Joint Task Force transformation initiative[/reference]
The Core
The framework core outlines a set of activities designed to achieve specific cybersecurity outcomes, and provides examples of steps that can be taken to meet these goals. The core is organized into four tiers: functions, categories, subcategories, and informative references. At the highest level, the functions organize basic groups of cybersecurity activities. They include Identify, Protect, Detect, Respond, and Recover. The remaining elements align with these functions. The categories are subdivisions of the functions that reflect particular needs or activities, such as “asset management.” The categories are then divided into subcategories with more specific technical or management activities. Finally, the informative references include current industry standards, guidelines, and practices that can be used for guidance. (See Table 1 for an overview of the core functions and categories.)
For example, the Protect function (abbreviated PR) leads to the Access Control category (AC). PR.AC states, “Access to assets and associated facilities is limited to authorized users, processes, or devices, and to authorized activities and transactions.” This general goal takes us to one of the PR.AC subcategories, PR.AC-1, which offers specific steps: “Identities and credentials are managed for authorized devices and users.” The informative references column then lists chapter and verse from relevant guidelines, standards, and practices associated with this subcategory line item. (See sidebar for the list cited in the framework)
At the NIST Web site, you’ll also find a tool the agency has developed that includes all the informational references. It is an easy way to keep this information handy and also includes a search function to dive into the grim details. It deserves a look.
Framework Implementations Tiers
The Tiers evaluate the steps taken by an organization to manage cybersecurity risk and how they comply with the risk management practices defined in the framework. The tiers characterize an organization’s practices over a range of responses, reflecting a progression from informal, reactive responses to agile, risk-informed approaches. They include Partial (tier 1), Risk Informed (tier 2), Repeatable (in terms of response, tier 3), and Adaptable (tier 4). When determining the tier level, an organization should consider not only its resources (manpower and financial) but also its tolerance of associated risk. In the NIST framework, each tier is further defined by the levels of risk management and participation with external partners to ensure that accurate information is being distributed.
Profiles
Finally, the profile summarizes the outcomes that an organization has selected from the framework core. Profiles can be used to describe and detail an organization’s current state of cybersecurity, or be adjusted to define the preferred or future state. This tool can set a target to shoot for when making your cybersecurity framework more robust.
NIST does not go into a lot of detail on how to use profiles to rate and prioritize the subcategory items. One of the best methods I have seen is from management consulting firm Booz Allen Hamilton. The company’s short white paper “Implementing the Framework Profile” quickly shows how this can be done.3
According to the Booz Allen method, simply rate each subcategory line item based on your intended use (in other words, set your target scores). Add a column to the table to contain a score for each. Use the following rating system: 0 for “does not exist,” 25 for planned implementations, 50 to indicate that the planning and design stage is complete, 75 for partial implementation, and 100 for full implementation. Then add another column to show which stage you’re currently in. This way, you can rank the topline items and prioritize the work needed to achieve the target scores. The company also has a method to set relative importance.
It should be obvious by now that constant vigilance is needed when it comes to cybersecurity in healthcare IT. The NIST framework is a great place to start. But the details offered by HITRUST might be more in tune with the healthcare industry, as we’ll see in part 2 of this series. Stay tuned!
Jeff Kabachinski is a healthcare IT pundit and technical strategist in Davidson, NC. For more information, contact chief editor Jenny Lower at [email protected].
References
- Executive Order 13636: Improving Critical Infrastructure Cybersecurity of February 12, 2013. Washington, DC: Federal Register, Volume 78, Number 33, February 19, 2013.
- National Institute of Standards and Technology. Framework for Improving Critical Infrastructure Cybersecurity. Available at: http://nist.gov/cyberframework/upload/cybersecurity-framework-021214.pdf.
- Booz Allen Hamilton. NIST Cybersecurity Framework: Implementing the framework profile. Available at: http://www.boozallen.com/insights/2015/07/nist-cybersecurity-framework.
Photo credit: © Binu Omanakkuttan | Dreamstime.com