Keeping up with the increasing number of digital technologies and connected devices in hospitals requires a joint effort. Here are some tips.
By Melanie Hamilton-Basich
We live in an increasingly digital world. Nowhere is this more evident than in healthcare, which has seen an influx of connected devices in recent years—due, in large part, to the COVID-19 pandemic—and thrust healthcare technology management (HTM) professionals into the spotlight.
But keeping up with the rapid pace of technological advancements is no small task—and it requires collaboration among industry stakeholders due to device interconnectedness. To keep operations running smoothly, HTM departments must tackle diverse issues, including cybersecurity, interoperability, asset management, and staffing and training.
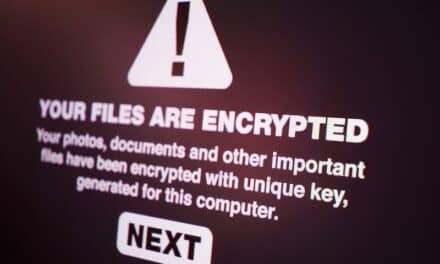
Being Cyber-Aware
Many people don’t fully comprehend the adverse impact one vulnerability can have on hospital operations, and on the function of medical devices, in particular. It’s now widely acknowledged that ransomware and other types of cyberattacks on hospitals and healthcare providers are increasingly common and pose a great risk to data integrity and patient safety. But most people don’t think about the possibility that they might be the ones to accidentally create the vulnerability that would lead to a breach.
It’s a modern marvel how easy it is to connect a medical device to a healthcare organization’s network. But it’s also one of the major problems with increased digital technologies. In fact, it’s what most worries many in the HTM field.
One major concern is someone from the outside, such as a vendor, connecting a device—medical or otherwise—without the IT department’s knowledge. If they’re not aware of it, they don’t have the chance to make sure it’s “hardened,” and not a cybersecurity threat, says Eddie Myers, director of cybersecurity for Crothall Healthcare, which provides HTM support solutions to healthcare providers.
“Then [this person is] able to jump on to guest Wi-Fi or just an open Wi-Fi network, and now that medical device is on the network,” Myers says. “And with the rapid increase of medical devices, it really does scare me.”
Another concern is the way medical devices themselves are designed and manufactured, he says. Incorporating services that are not “closed” can pose a cybersecurity threat.
“I don’t know how many medical devices out there have Internet Explorer or Google Chrome, and there is no clinical reason for them to have that,” Myers laments. “That’s what keeps a lot of us up at night.”
Again, if anyone in the hospital checks their email or social media account using one of these programs, it could expose all the data and devices connected to a hospital’s network to bad actors.
New Security Requirements for Medical Devices
But that should begin to change now that the U.S. FDA is requiring new medical device applicants to follow updated cybersecurity guidelines, per the agency’s March guidance. Companies must submit a plan for how to “monitor, identify, and address” any cybersecurity problems, as well as provide security updates and patches on a regular schedule and as needed for emergencies. Perhaps most importantly, applicants must submit to the FDA a software bill of materials, or SBOM, detailing what software the device uses, including open-source software.
“It’s going to greatly help in holding the OEMs accountable, to not only design some of the best medical devices, but to keep cybersecurity in mind,” says Myers. “It will really help us [healthcare technology officers] working with the OEMs on patches and all other mitigating steps.”
What IT and service technicians need to keep in mind is that these requirements only apply to medical devices submitted to the FDA very recently and in the future. In the meantime, the same cybersecurity concerns exist for all devices submitted before these guidelines went into effect, including many still in development and all medical devices currently in use.
“But moving forward, it’s really going to help with new equipment installed and approved,” Myers says.
Vetting Everything Before Implementation
Which devices have vulnerabilities? Potentially all of them. That’s why it’s so important to vet everything before, during, and after installation, experts say. And nowadays, that doesn’t just mean medical equipment, such as ventilators and infusion pumps. Anything connected to the network can be problematic.
As the director of IT and biomed services for Providence Medical Institute’s St. Mary Medical Center in Southern California, Doug Kleine oversees not just equipment maintenance, but the entire medical center’s IT infrastructure. So he has a vested interest in making sure all of the digital components of the hospital system operate properly and securely.
“With the IT and biomed worlds now crossed over, this is no longer just an IT concern,” Kleine says. “Devices and software both are scrutinized for cybersecurity.”
Kleine’s organization has successfully expanded its range of digital products in recent years, encompassing call center software, digital hand-hygiene tracking technology, and most recently, a monitoring system aimed at reducing hospital-acquired pressure ulcers. In addition, his team has significantly improved their evaluation process for these and any future technologies to be implemented within their health system, ensuring thorough scrutiny before network integration.
“We look for things like unique passwords and accounts for each user, data encryption, back doors, accessibility over the internet, up-stream and down-stream dependencies, life span, and more,” he says.
After all, Kleine says, digital technologies have transformed how healthcare does business. “We all like to use technology to help improve patient safety, to improve caregiver and physician satisfaction,” he says. “But without a cybersecurity deep dive into the products and vendors we use, these new technologies could be more dangerous than helpful.” The moral of the story, according to Kleine? “Know what you’re implementing.”
Catching Problems as They Arise
Just because a device or software is new—even if it’s been found to be cybersecure before implementation—doesn’t mean that it won’t develop vulnerabilities. “One of the big misconceptions people have is thinking that newer devices are more secure than older devices,” says Myers. “With all of the vulnerabilities that are released monthly, you may have a brand-new device with the latest operating system, and within a month, if you’re not patching it, it’s just as vulnerable as any other device.”
Because of this, it’s important to constantly monitor devices and other digital solutions for cyber vulnerabilities. And much older legacy devices can pose their own problems, such as running on operating systems like Windows 7 that are no longer supported. But because healthcare organizations have limited resources, and because biomeds have become so good at prolonging the service life of medical equipment, it’s common for “legacy” devices to be used for quite some time. And IT professionals and biomeds will have to make do for the length of a device’s service life.
“You can have a passive asset discovery tool that can also perform active exploit analysis and vulnerability analysis to [help] determine what services can be disabled. To further secure that legacy device, you can segment the device—so it only talks to what it absolutely has to talk to on certain ports,” says Myers. “That definitely helps reduce the footprint of vulnerabilities.”
But the tools are only part of the solution, he emphasizes. You need to hire people who know how to mitigate these problems—and quickly. Which also means ongoing training to maintain these skills is essential.
“With a lack of [staffing], it’s difficult to address medical devices quickly enough,” worries Myers. “Even when you have a [vulnerability analysis tool], who is managing it? Is it IT? Clinical engineering? You need to ramp up the workforce, so that not only do you have the tool [to alert you to cybersecurity vulnerabilities in devices], but you also can remediate those devices.”
And it’s not enough to have excellent technicians. There are very skilled IT professionals, and there are very skilled biomeds, yet they often don’t share knowledge of each other’s specialties or of many things outside of their wheelhouse, which poses a major problem when a cybersecurity crisis occurs.
“So, you have to have someone who can sit in the middle and understand the medical devices, the regulations that they operate under, and also be able to understand IT, cybersecurity, and all the stuff that comes with that,” says Myers. “Really trying to fill that gap is the key part.”
The Importance of Interoperability in Digital Technologies
Cybersecurity is certainly important to a healthcare organization’s operations, but it’s not the only issue that affects HTM professionals when it comes to digital technologies.
Even if every medical device is somehow perfectly secure and protected from cyber threats, if the organization’s equipment and systems don’t work together and provide necessary information, they’re not very useful—to staff or to patients. That’s why interoperability is so important.
It’s something HTM veteran Paul Sherman knows all too well. He has seen just how much the industry has changed in the past 30 years and how using the same communication standards can streamline the way healthcare systems share information. As the program manager for IHE International Patient Care devices, he “managed the project to get the medical equipment talking to the other hospital systems,” he explains.
His role at IHE (Integrating the Healthcare Enterprise) involved meeting with companies and other stakeholders to coordinate implementation of the established HL7 standard to facilitate this process, one of the initiative’s goals. But it’s still very much a work in progress, Sherman acknowledges.
How It Should Work
IHE has established guidelines for how to implement HL7 standards that would allow medical devices to automatically report data such as their location, self-test results, and software update status through a streamlined system that could enter it into the equipment record on its own. But because not enough companies have agreed to participate, it’s not working the way it could, some maintain.
Many companies say they already comply with HL7 standards and see no reason to change their practices. But the issue is one of compatibility, others maintain. Companies must adhere to the specific guidelines set by IHE for their messages to be recognized and data to be successfully transferred, regardless of whether they are following general standards.
“Unless you get the two companies to sit down with each other and say, ‘OK, this is where this piece of information’s going to be in the message, and this is what it’s going to say and this is how it’s supposed to look,’ then the communication just doesn’t happen,” Sherman says. “It’s kind of like the difference between British English and American English.”
Barriers to Implementation
Currently, medical equipment companies are following agreed upon protocols for how to use HL7 to transmit data from their products, but most equipment management software companies are not, Sherman says. This means data about a medical device cannot automatically get reported in the equipment’s record. People must, instead, manually report this information when they get around to it, which greatly affects BMETs.
“A biomed is getting all secondhand information, and it’s delayed,” says Sherman. “If a piece of equipment goes through the self-test and has a problem, it could send a message to the maintenance management system, saying, ‘Hey, I’ve got an issue; I need somebody to look at me,’” but that’s not what’s happening. Instead, he says, if a nurse realizes they need another infusion pump, they’ll shove the one not working off to the side, find another pump to use, and report the issue when they get a chance.
“You could run the tests on your infusion pump from the test equipment and it could dump that information directly into the equipment’s record,” Sherman says. “The same [goes] for equipment location. Many asset-tracking companies are interested.” But without the cooperation of the equipment management software companies, it’s unttainable.
“They don’t even have to join IHE,” says Sherman. “They just have to implement the IHE protocol.” The benefits, he contends, would be numerous. Improved asset tracking that includes information on device updates and recalls could reduce paperwork, save time, and improve patient outcomes, he explains.
Be the Change
They say the only constant is change. That’s why it only makes sense to advocate for policies that will allow the industry to pivot when necessary, proponents say.
“Today, if we could get the equipment management software companies and the test equipment vendors to participate, that would provide real, tangible benefit to those in HTM,” says Sherman of IHE’s interoperability initiative.
He hopes more techs will become involved with IHE and provide input about how using the streamlined HL7 standards would help them. He also recommends that they talk to hospital management and any vendors they work with that are not yet participating to convey what a boon true interoperability would be to everyone in healthcare.
For his part, Crothall’s Eddie Myers also recommends getting involved in groups that can make a positive difference in the HTM field, such as the Healthcare Sector Coordinating Council, of which he’s a part. He knows that cybersecurity concerns will continue to change, as will the profession.
“Our industry is reportedly aging out right now, and we have a shortage of talented professionals. That does worry me,” Myers says. “But I’m cautiously optimistic that the shortage will eventually become less severe. And with new technicians coming in, understanding IT, and filling that gap, it’s definitely going to be key moving forward.”
In other words, digital technologies will continue to impact HTM. The key lies in adopting the right approach to tackle this challenge.
Melanie Hamilton-Basich is managing editor of 24×7. Questions and comments can be directed to [email protected].